How is ssh different from telnet
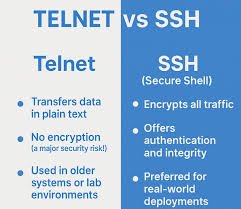
The primary difference between SSH and Telnet is that SSH encrypts all communication, providing a secure connection, while Telnet sends all data in plain text, making it highly vulnerable to interception and security attacks. SSH is the modern, recommended standard for remote access, whereas Telnet is largely obsolete due to its security flaws.
Comparison of SSH and Telnet
| Feature | SSH (Secure Shell) | Telnet (Telecommunication Network) |
|---|---|---|
| Security | Encrypts all data transmitted, ensuring confidentiality and integrity. | Transmits all data in plain text, making it vulnerable to eavesdropping. |
| Authentication | Uses strong authentication methods, including passwords and public-key cryptography. | Uses basic username/password authentication, which is sent unencrypted. |
| Default Port | Uses TCP port 22 by default, which can be changed. | Uses TCP port 23 by default, which is not typically changed. |
| Use Case | The standard for secure remote server administration, file transfers (SFTP/SCP), and tunneling over public networks like the internet. | Primarily used for testing network connectivity, in isolated, trusted local area networks (LANs), or for legacy devices that don’t support SSH. |
| Complexity | Involves more complex setup for features like key-based authentication. | Simple and minimal setup required. |
Summary of Key Differences
- Encryption: The most critical difference is that SSH provides robust encryption, while Telnet offers none. This means sensitive information like usernames and passwords can be easily captured by an attacker using Telnet.
- Security Posture: SSH was developed in 1995 specifically to address the security vulnerabilities of older protocols like Telnet and rlogin. Telnet was designed in 1969 when networks were considered private and security was not a primary concern.
- Functionality: Beyond secure remote command-line access, SSH supports features like secure file transfers (SCP and SFTP) and secure port forwarding/tunneling, which Telnet does not natively support.
In modern networking, SSH is the only recommended choice for any scenario where data security and privacy are important.