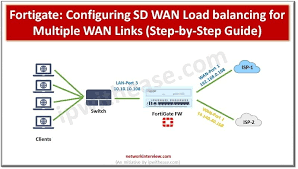
How to configure load balancer in fortigate firewall
Configuring a load balancer in a FortiGate firewall involves enabling the “Load Balance” feature in System > Feature Visibility, then defining a Virtual Server under Policy & Objects to act as the public-facing IP. You must assign a load-balancing method (e.g., Round Robin), add real servers with their IP addresses, configure a health check, and finally, create a firewall policy to…